Ransomware extortion site seized by law enforcement
10/22/2023Darknet News
The Tor negotiation and data leak sites for the Ragnar Locker ransomware campaign were taken down on Thursday morning as part of an international law enforcement investigation.
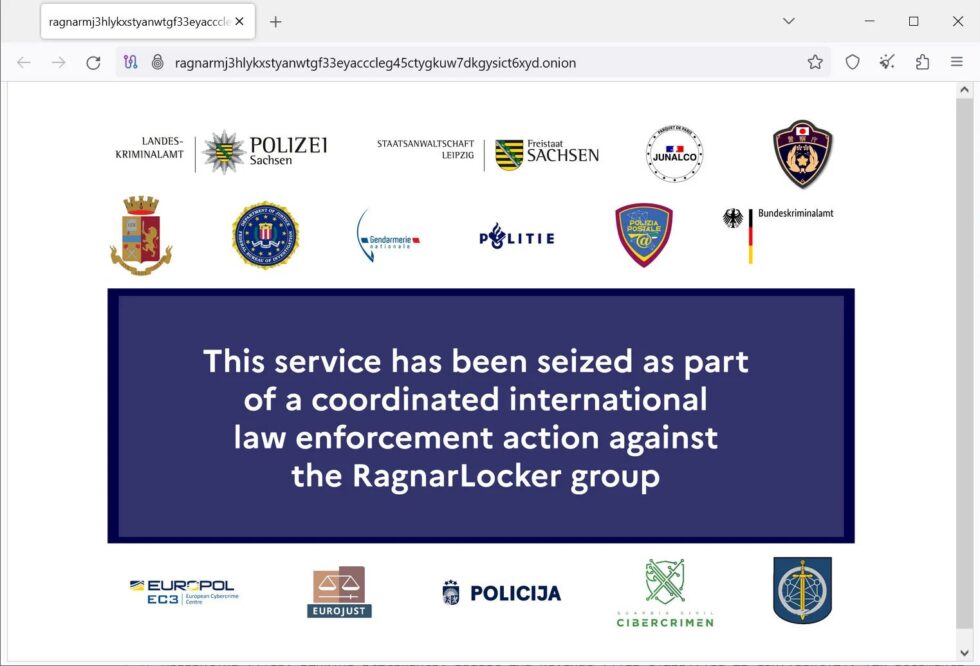
A seizure statement claiming that a big number of international law enforcement from the US, Europe, Germany, France, Italy, Japan, Spain, Netherlands, Czech Republic, and Latvia were part in the operation is now displayed when visiting either website, according to BleepingComputer.
“This service has been seized as part of a coordinated law enforcement action against the Ragnar Locker group,” the message begins.
A spokesman for Europol has stated that a press statement will be released tomorrow and that the seizure message is authentic and part of an ongoing operation against the Ragnar Locker ransomware gang. The FBI chose not to respond.
One of the longest-running ransomware operations at the moment, Ragnar Locker (also known as Ragnar_Locker and RagnarLocker) launched toward the end of 2019 when they started focusing on the enterprise.
Ragnar Locker operated similarly to earlier ransomware attacks by infiltrating business networks, spreading laterally to other devices while gathering data, and finally encrypting the computers connected to the network.
In double-extortion methods, the encrypted files and stolen data were utilized as leverage to put the victim under financial pressure.
Ragnar Locker, however, was not regarded as a Ransomware-as-a-Service that actively recruited outside affiliates to hack networks and install the ransomware while receiving a revenue share.
Instead, Ragnar Locker operated in a semi-private manner, relying on independent pentesters to break into networks rather than actively recruiting affiliates.
Instead of utilizing an encryptor, the ransomware group also carries out straightforward data theft attacks, using its data leak site to blackmail the victim.
RagnarLocker has more recently shifted to employing a VMware ESXi encryptor built using Babuk’s released source code, claims cybersecurity researcher MalwareHunterTeam.
But in an attack on industrial behemoth Johnson Controls, a fresh ransomware operation known as DarkAngels was observed using Ragnar Locker’s original ESXi encryptor.
It’s unclear whether this new business is a spinoff of Ragnar Locker, a rebrand, or if the source code was purchased.
Over the years, the ransomware operation has been behind a number of notable assaults, including those on Energias de Portugal (EDP), Capcom, Campari, Dassault Falcon Jet, ADATA, and the Belgian city of Antwerp.
In contrast to ransomware operations, this week has been successful for law enforcement and cybersecurity. The Ukrainian Cyber Alliance (UCA) also hacked the Trigona Ransomware operation and recovered data before erasing their servers, in addition to the RagnarLocker seizure.