Akira Ransomware Group Threatens to dump Stanford Data
10/30/2023Cybercrime
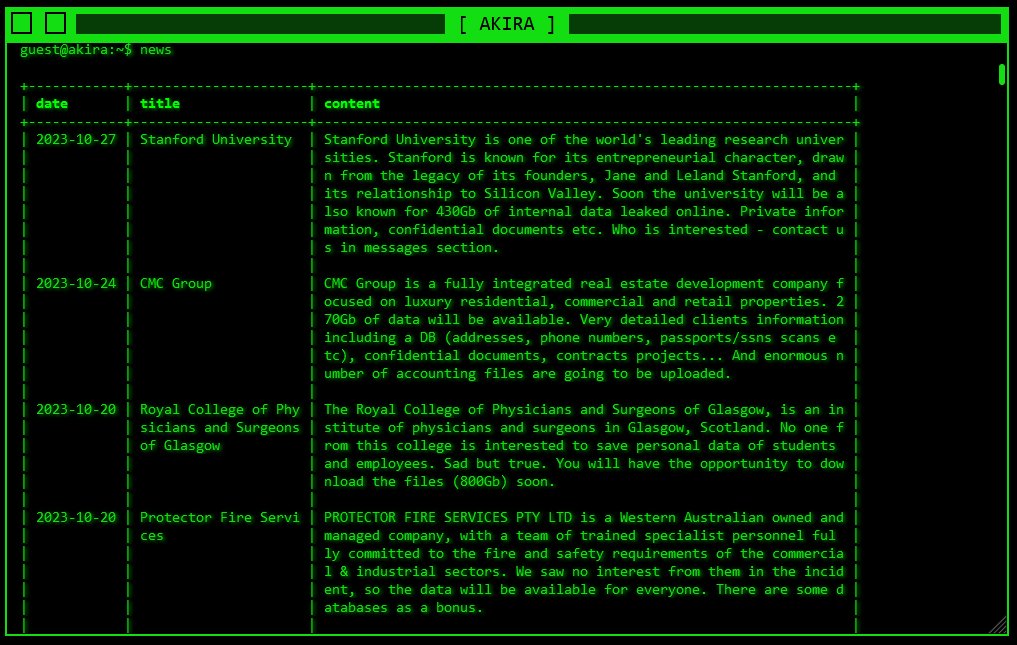
Stanford University was reported as the target of a ransomware attack on the darknet on Friday morning by the infamous ransomware group “Akira.” Cyber risk analyst Brett Callow posted screenshots of the listing on X (formerly Twitter) and the r/stanford subreddit, among other websites.
Akira states that it has 430 gigabytes of internal data, which includes private and sensitive documents. If the University did not pay an unidentified ransom, they threatened to post the information online.
The Department of Public Safety at Stanford University handles and maintains information about staff, case studies, risk assessments, and crimes against students, faculty, and other community members. How much of this data was destroyed or encrypted by this ransomware is unknown at this time.
“There is no indication that the incident affected any other part of the university, nor did it impact police response to emergencies,” the university said in a statement released on Friday. In line with the statement, “we will act accordingly and be able to share more information with the community once the investigation is completed.”
Stanford is “known for its entrepreneurial character,” according to the Akira listing. “Soon the university will be also known for 430Gb of internal data leaked online,” the group threatened. Documents that are sensitive and private.
The University of California, Berkeley’s Chris Hoofnagle, a law professor and the head of the Center for Law & Technology, stated in a letter that attackers that target law enforcement agencies are occasionally “a nation state or organized crime” organization.
It can be costly and time-consuming to identify the extent of the breach in the first place. Hoofnagle wrote, “Almost all entities contract with independent forensic firms to perform the analysis.
According to what he wrote, it was “best practice” to withhold information until the network was secure and the entire extent of the intrusion was known. Institutions don’t want to find themselves in a scenario where they have to keep notifying people about breaches after discovering that the breaches were worse than they initially thought, according to Hoofnagle.
Hoofnagle wrote after the listing, “Stanford could pay the ransom— many companies do.” If students thought that their personal information was compromised, he suggested that they file a security alert.
The term “Akira” describes a family of ransomware that was first discovered in March 2023 and has been linked to over a dozen attacks on American and Canadian companies.
The gang consistently publishes data online in the event that ransom payments in the range of $200,000 to $4 million are not made.
The darknet website also acts as a central location for information regarding previous leaks and impending disclosures. Through magnet links, which anonymously link you to other network users who distribute the file directly, you can obtain data from past victims. Since March, Akira has listed over 60 institutions, including Mercer University in Georgia and the American energy business BHI.
Significant links were found between Akira and Conti, a different ransomware that was originally discovered in 2020 and is thought to be propagated by a gang located in Russia, according to cybersecurity companies including Avast and Arctic Wolf. According to investigations, the following communication was sent to compromised entities:
“If you are reading this, it indicates that your company’s internal infrastructure is either completely or partially dead. All of your backups, both virtual and real, that we were able to access, have been erased. Please let us know who you are and what title you hold. Additionally, a significant portion of your company data was obtained by us before it was encrypted.
Dee Mostofi, a spokesman for the university, said that the investigation is still ongoing. “In collaboration with external experts, the University’s privacy and information security teams have been providing this issue with their full focus,” Mostofi stated.
Potential liabilities were covered on Saturday by The Palo Alto Daily Post. “Someone could sue Stanford if they have sealed arrest records or body camera footage that gets leaked,” cybersecurity expert Ahmed Banafa said. Many prominent, significant, and influential Stanford alumni may not wish to be made public.
In response to worries expressed on the University IT Slack Channel, Noah Abrahamson, director of cloud security and information security office operations, affirmed that his team was “aware” of the listing.
When contacted for a response, SUDPS pointed The Daily toward the University statement.